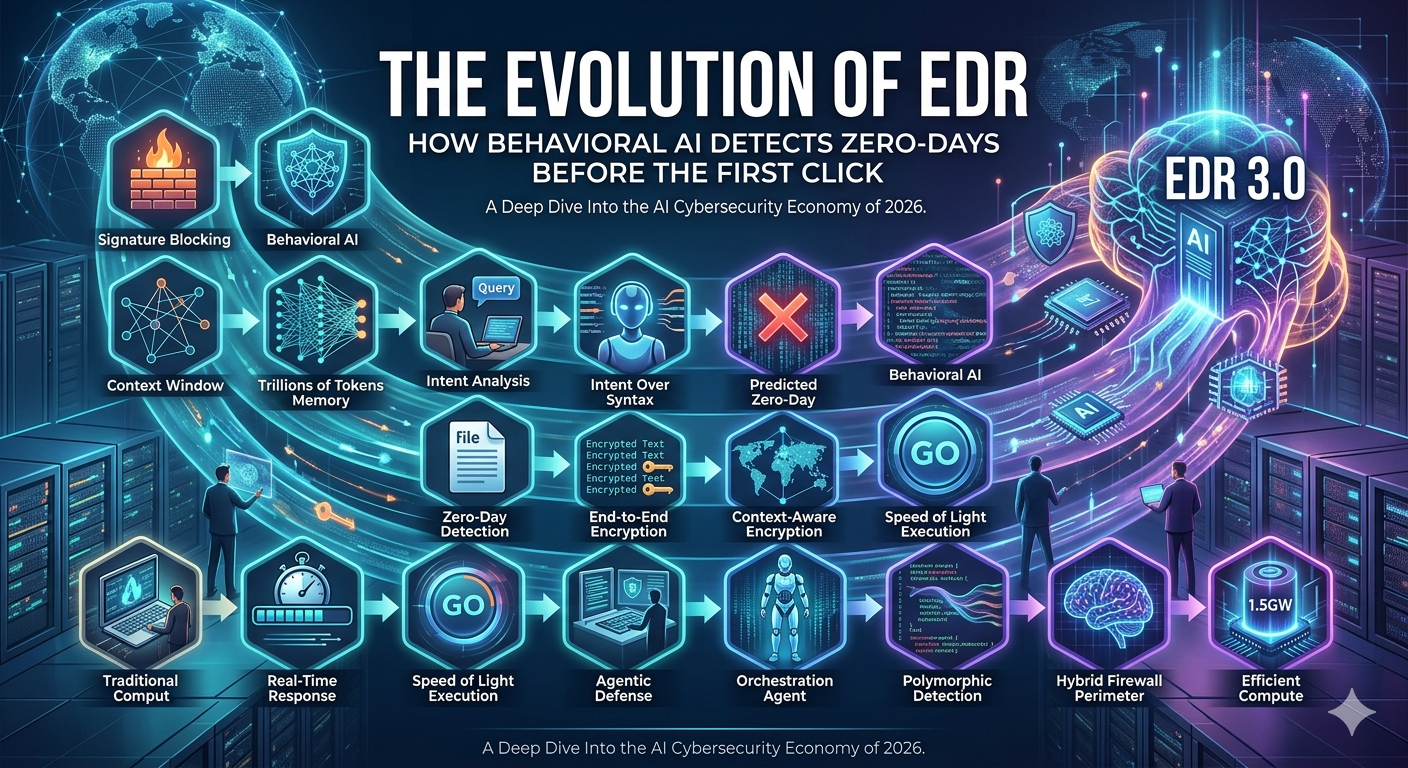
The Evolution of EDR: How Behavioral AI Detects Zero-Days Before the First Click
Introduction
Cybersecurity has entered a new era. Traditional defenses—built around signatures, known malware, and reactive responses—are no longer enough.
Today’s threats move faster, mutate constantly, and often exploit vulnerabilities that have never been seen before.
This is where EDR (Endpoint Detection and Response) has evolved—and more importantly, where behavioral AI is changing the game.
Instead of waiting for an attack to happen, modern systems can now detect and stop zero-day threats before a user even clicks a malicious link.
What Is EDR?
EDR (Endpoint Detection and Response) is a cybersecurity solution designed to:
Monitor endpoint activity (laptops, servers, devices)
Detect suspicious behavior
Investigate threats
Respond in real time
Unlike traditional antivirus software, EDR doesn’t just scan files—it observes behavior continuously.
The Problem with Traditional Security
Legacy security systems rely heavily on:
Signature-based detection
Known malware databases
Rule-based alerts
This creates a major gap:
If a threat has never been seen before, it often goes undetected.
This is exactly how zero-day attacks succeed.
What Are Zero-Day Attacks?
A zero-day attack exploits a vulnerability that:
Is unknown to vendors
Has no available patch
Has no signature in detection systems
In simple terms:
You’re being attacked by something your defenses don’t even recognize yet.
The Shift: From Signatures to Behavior
Modern EDR solutions are moving away from:
“Is this file known?”
to:
“Is this behavior normal?”
This shift is powered by behavioral AI.
What Is Behavioral AI in EDR?
Behavioral AI focuses on patterns of activity rather than known threats.
It analyzes:
Process behavior
File access patterns
Network communication
User activity
System-level changes
Instead of identifying what something is, it identifies what something is doing.
How Behavioral AI Detects Zero-Days Early
Here’s how modern EDR systems can stop threats before execution:
1. Baseline Behavior Modeling
The system learns what “normal” looks like across endpoints:
Typical applications
Standard user workflows
Expected network behavior
Any deviation becomes suspicious.
2. Pre-Execution Analysis
Before a file is opened or executed:
The system analyzes its structure and intent
Predicts potential behavior
Flags anomalies
This allows detection before the first click triggers damage.
3. Real-Time Behavior Monitoring
If something starts behaving abnormally:
Unexpected privilege escalation
Unauthorized file access
Suspicious process chains
The system immediately raises alerts or blocks execution.
4. AI-Driven Anomaly Detection
Behavioral AI identifies patterns humans might miss:
Subtle lateral movement
Slow data exfiltration
Fileless attacks
These are often invisible to traditional tools.
5. Automated Response
Once a threat is detected:
Processes can be terminated
Devices can be isolated
Access can be revoked
All in real time—without waiting for manual intervention.
Real-World Example
Imagine an employee receives an email with an attachment.
Before they even open it:
The EDR system analyzes the file
Detects unusual code patterns
Predicts suspicious behavior
If the user attempts to open it:
The system blocks execution
Alerts security teams
Isolates the endpoint if needed
Result: The attack is stopped before it begins.
Why This Evolution Matters
Behavioral AI transforms EDR from:
Reactive defense → Proactive protection
Key benefits include:
Detection of unknown threats
Reduced reliance on signatures
Faster response times
Lower risk of breaches
Challenges and Considerations
While powerful, behavioral AI comes with challenges:
False positives if baselines aren’t well-trained
Complexity in tuning detection models
Need for continuous monitoring and updates
Organizations must balance automation with oversight.
The Future of EDR
The next generation of EDR is evolving toward:
Fully autonomous threat response
Integration with XDR (Extended Detection and Response)
Cross-platform visibility (cloud, network, endpoints)
Continuous learning systems
EDR is no longer just a tool—it’s becoming a self-adapting security layer.
How to Get Started
If you’re exploring modern EDR solutions:
Evaluate current security gaps
Look for behavioral AI capabilities
Start with pilot deployments
Train models with real-world data
Establish monitoring and response workflows
Conclusion
Cyber threats aren’t waiting—and neither should your defenses.
The evolution of EDR shows a clear shift:
From detecting known attacks to predicting unknown ones.
Behavioral AI enables organizations to stop threats before damage occurs, even when those threats have never been seen before.
In a world of zero-days, that’s not just an advantage—it’s essential.